A recent survey by IDG confirms, application whitelisting is by far the most underutilized component of zero-trust technologies.
What is Application Whitelisting?
Application whitelisting only allows known trusted, and proven secure applications to run on the network. This is an effective means to cyber threat mitigation because no matter how many times malware evolves, it will never be a known trusted program. Therefore, it would be unable to execute on a network that is using application whitelisting.
How Does It Fit Into Zero-Trust?
The idea of zero-trust architectures are just that; zero-trust. Until something or someone has been proven to be trusted, it will not be granted access. This may mean placing controls on applications, like application whitelisting, or deploying multi-factor authentication to authorize personnel access. Unfortunately the IDG survey confirmed application whitelisting has only been adopted by 32% of surveyed respondents.
The Looming Threat & Resistance to Prevention
With 62% of individuals believing their organizations will be hit with a cyber attack in the next twelve months, the question is, what will they do to prevent it? The reality is, many organizations are looking to zero-trust architectures to help bolster the integrity of their digital infrastructures. When zero-trust access features are combined with whitelisting, secure RDP, device authentication, driver updates, and security patch updates, endpoints and networks are better protected.
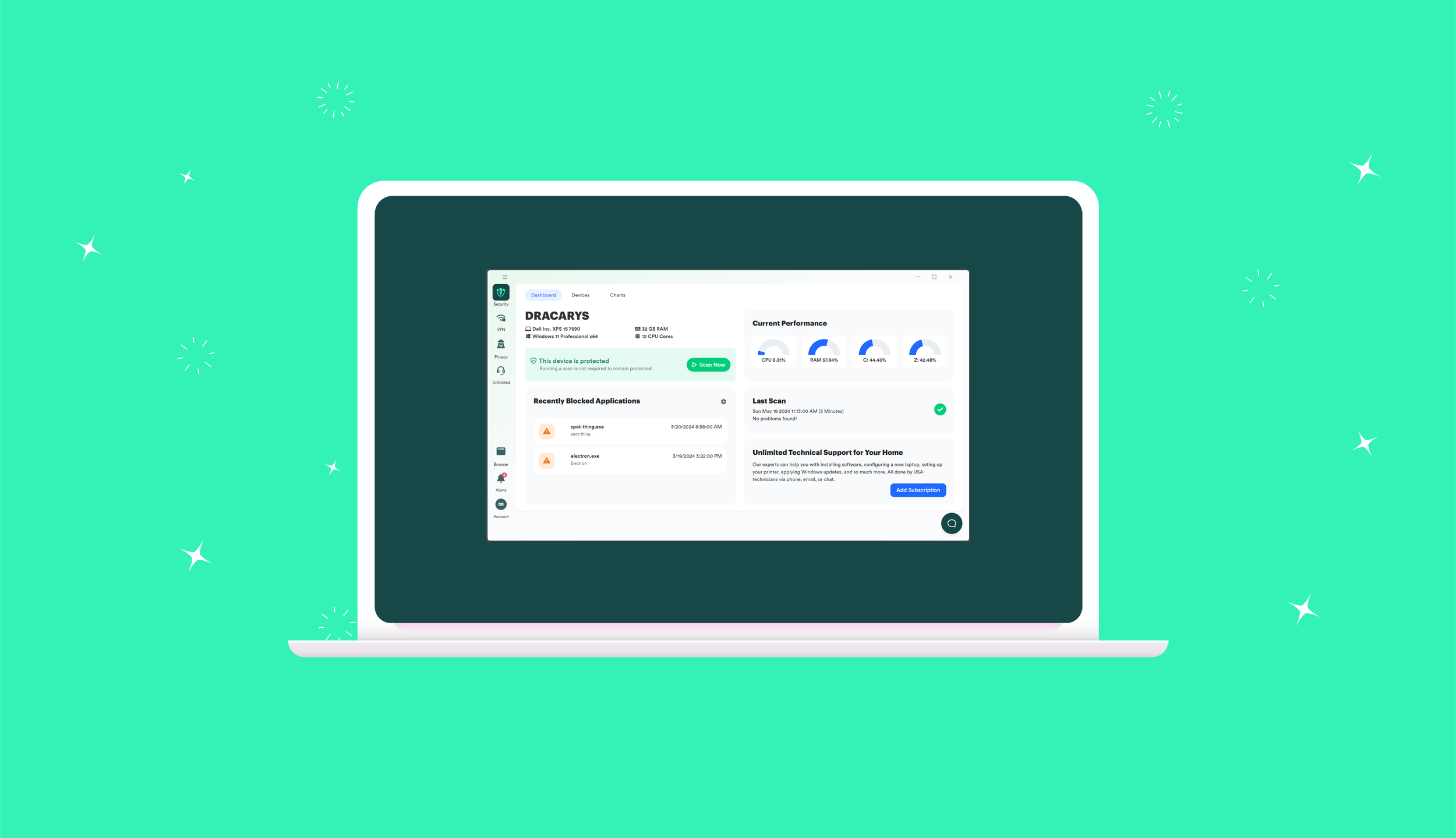
PC Matic offers Endpoint Security, Ransomware Protection, Network and Server Security solutions. Special business protection against ransomware can also be found in the Small Business Cyber Security solutions and Business Security Software with Application Whitelisting.
With application whitelisting being adopted by less than a third of respondents, the question is — what is the resistance? If application whitelisting is indeed the gold standard, as set by the National Institute of Standards and Technology (NIST), FBI, and Department of Homeland Security, why isn’t there a higher adoption rate? Some of the reason may lie in that many IT professionals are more familiar with Application Control vs Application Whitelisting.
AWL is Recommended by NIST
AWL Security Software is a recommended practice by the NIST together with zero trust access. PC Matic offers a global whitelist that makes it easy for IT administrators to set up their network to work quickly with whitelist protection. Working with whitelisting best practices ensures only programs that an administrator trusts can run. Any other script or process will not gain access to run on the system.
PC Matic’s Mission with NCCoE
The lack of adoption why PC Matic applied to collaborate with the NIST National Cybersecurity Center of Excellence. By joining NCCoE, PC Matic will be working hand-in-hand with this organization, as well as several other vendors, to develop a practice guide to deploying all aspects of zero-trust architectures, including the adoption of application whitelisting.
This is a big step for PC Matic, and their drive for prevention. Great things are soon to come!