Implementing robust and proactive security measures is crucial to effectively prevent and counter zero-day vulnerability attacks
Real-time vulnerability threat intelligence enables you to swiftly shift focus to plan strategies for mitigating and addressing these vulnerabilities
Deploys a critical preventative layer of cyber-protection that can reside on top of other endpoint security solutions without introducing headaches for IT
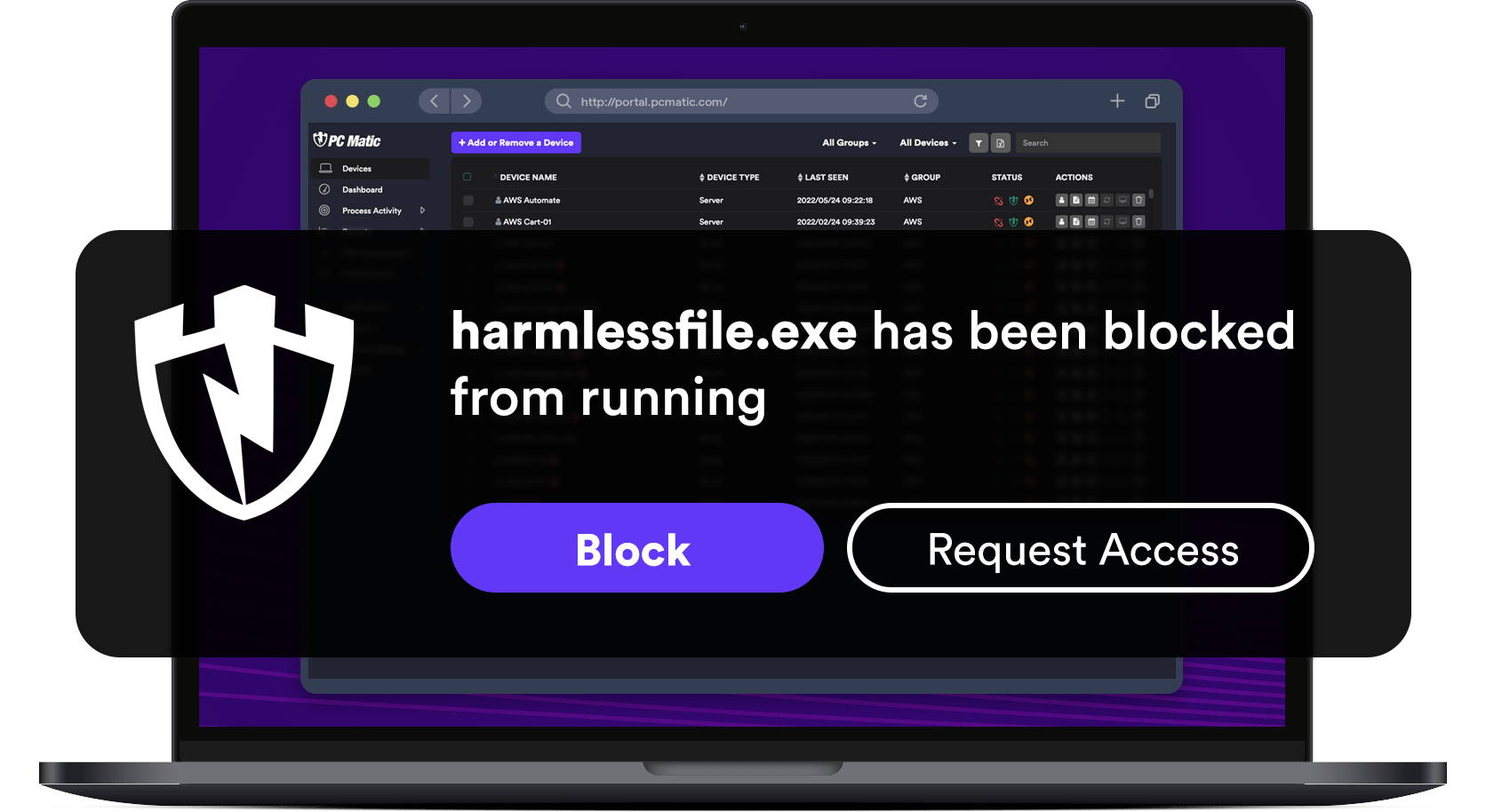
PC Matic's Application Allowlisting is a digital security technology which only allows trusted files and scripts of a known, good application to run on a system or device. PC Matic monitors an operating system in real-time to uniquely identify and screen each file regardless of what software publisher, parent process, or software package it belongs to. This deeper level of cyber-protection, also referred to as entity integrity monitoring is combined with real time allowlist updates, PowerShell script use restrictions, and secure RDP monitoring.
Application Allowlisting provides greater security.
Application Allowlisting technology is implemented differently than Application Control although the terms are many times used interchangeably by IT professionals when discussing system security. Application Allowlisting provides greater cyber-protection. PC Matic's Application Allowlisting does not trust a script or file simply because it is part of a known or trusted legitimate application. Application Control, on the other hand may allow that same file or script to run simply because it is attributed to a known or trusted legitimate program. While allowlisting also places full control over which applications are permitted to run on a user's device, server or network, it does so by detailed malware screening of each and every file, script, macro, process, and file extension, not just every program.
PC Matic fully integrates advanced application control with zero trust network and endpoint security, ransomware protection, blacklist antivirus, secure RDP, automated driver updates, and security patch management.

The goal of Application Allowlisting is to protect computers and networks from malicious applications by not allowing cyber-criminals to place their own executables on the system or device. This includes bad actors disguising and replacing known good executables with compromised ones to launch a cyber-attack. Application Allowlisting also prevents zero-day attacks by not allowing the execution of any non-allowlisted or un-trusted applications, scripts, installers or macros.
Having the right Application Allowlisting tools, like PC Matic, in place is the key to ransomware prevention especially when running brand new, unknown or non-trusted applications.





Application Allowlisting provides granular protection at the file, script, and process level. In comparison, Application Control identifies or flags entire application packages by focusing on whether a program is known and trusted, as opposed to focusing on each and every file including scripts, macros, processes, and file extensions.
Screening with Application Control does not take place at the granular file and entity level as it does with AAL. So while Application Control will flag and block "unrecognized software changes", Application Allowlisting will flag and block any file, script, file extension or macro changes.
Application Control can allow files from a trusted application to run. It checks to see if anything has changed since the program was initially installed. While this ensures some level of system security, it does not prevent many sophisticated types of modern malware from penetrating a system.
Modern malware including ransomware is written to avoid application level screening. Files, scripts, macros, and even security updates can be disguised as belonging to an application package. Malicious code can piggyback on seemingly legitimate software program updates and downloads. A better solution to combat these kinds of modern cyber-threats is Application Allowlisting (AAL) which screens all device and system files even those from trusted applications.
Our team of cybersecurity professionals will assess your current security posture and help you to implement a complete security solution for a fully protected, secure server and network. Our zero trust solutions can be utilized across hybrid environments including cloud-hosted virtual machines to protect servers, applications and databases.
With Application Allowlisting, if any file, script, macro, driver, or security patch update is unknown, modified or not already on the approved allowlist, that file or script is prevented from executing by default. It doesn't matter if the application itself is known and trusted.
This is where Application Allowlisting for cybersecurity effectiveness really shines vs Application Control, Blacklisting Antivirus or zero trust measures alone. The granularity of file, script and macro inspection differentiates Application Allowlisting from App Control making Application Allowlisting superior in providing protection against malware and ransomware attacks.
Application Allowlisting for Server Security comprises the comprehensive IT safeguards and application control tools used to protect data and IT assets on an organization's servers.
Unified Network Performance Monitoring provides a unified security view of your IT environment including hybrid and cloud networks to detect threats and performance issues in real time across all your applications.
Allowlisting solutions and security tools are superior because they stop malware or threat actors from even running their malicious code on your network or device. Typical blacklist antivirus programs wait until a machine or system is infected, or a vulnerability is reported to add malware to their blacklists.Allowlists are malware prevention tools; Blacklists are malware reaction tools.
IT Networks and Servers are the most frequent targets of cyber-criminals looking to exploit vulnerabilities in a system's security to disrupt operations, steal data, or to ransom critical company data. Do not become a victim of a ransomware attack. Harden your network or cloud servers with the best automated application allowlisting tools available in the USA.