A Five Step Program
Staying secure in our current online environment is a continually pressing concern. There’s a balance between locking down your entire system for security and still being able to do what you want online. Luckily, there are five steps you can take to make sure you’re keeping yourself safe.
Step 1
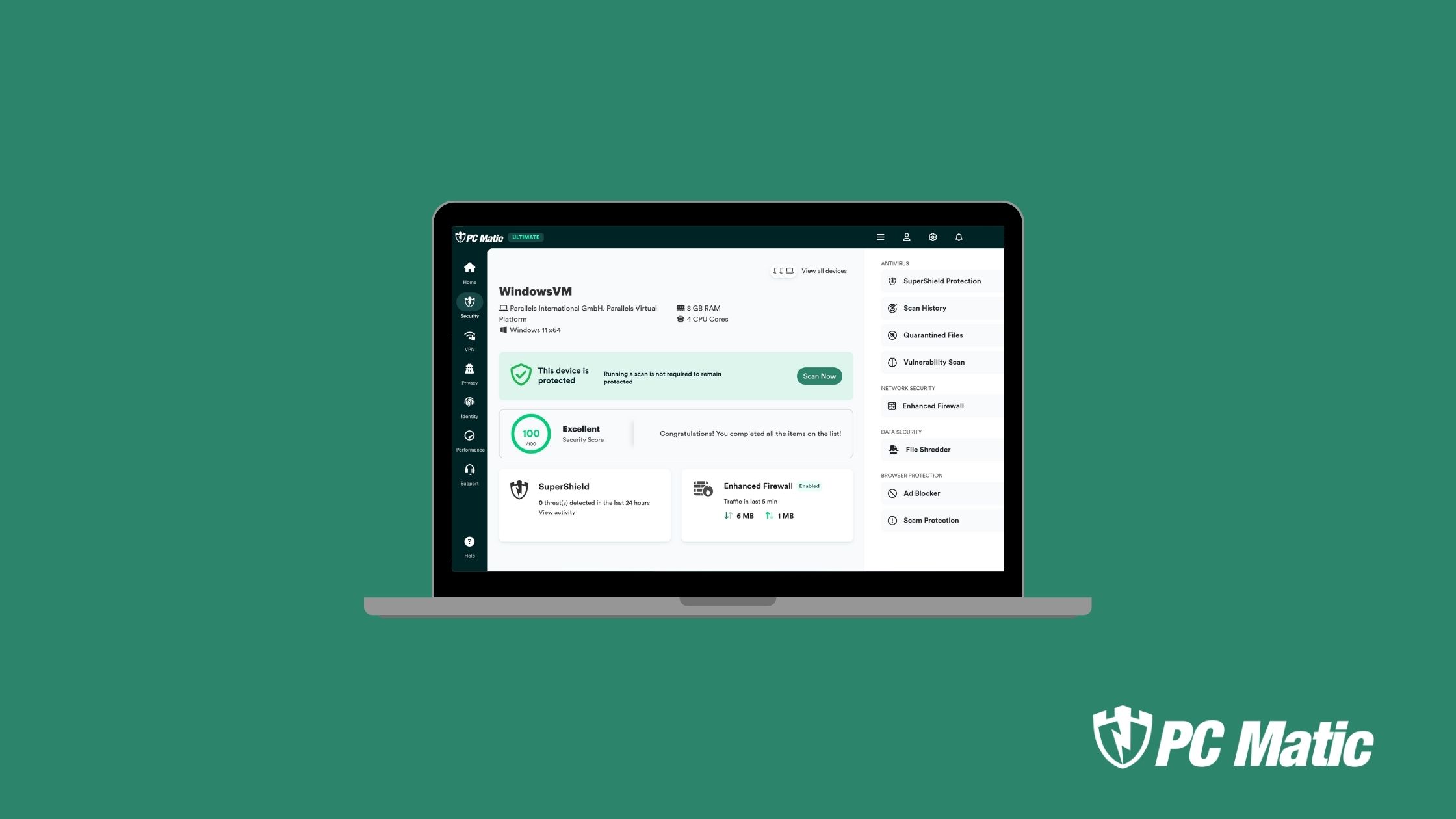
You have to evaluate your security product. There’s no way around it. All those pre-loaded antivirus programs that came with the purchase of your new PC in the 90s are still working the same way. Even if you upgraded with the same company and bought a fancier plan, they’re still using blacklist technology.
As we’ve mentioned here in TechTalk ad naseum, blacklisting is going the way of the Dodo. We all know what’s recommended, so let’s start by cleaning up your security product. Go for whitelist technology and sleep sound knowing the things that go bump in the dark (web) aren’t going to be authorized to download onto your machine.
Step 2
Patch those holes! Make sure you’re running the latest updates on your operating systems and third party applications. It’s essential to keeping ahead of security breaches. Each update released
The software developers don’t release updates to annoy your or take a minute out of your day with an update. They’re constantly researching and testing holes in your security armor. Each update is a way to patch those holes.
Step 3
Education is power. Know how to spot red flags so you can better arm yourself against online scams. Knowing what’s normal and what’s not could keep you from opening that attachment or clicking on that link. If you never open yourself up to the threat, you can’t get infected.
Step 4
Step number four is password hygiene. This is probably the second most ignored recommendation for safety. Your passwords should be a complex combination of capital and lower-case letters, numbers, and special characters. Make up a key phrase like, “my dog only eats ice cubes from the floor,” then translate it into letters and numbers.
Definitely don’t write the code down. If you’re forgetful, use a password vault (do a quick search to find the right one for you) which will keep all those passwords handy for you.
Finally, you’re going to want to update those passwords every six weeks. You’re either rolling your eyes or saying, “ha, no,” but seriously. With the amount of personal information being sold daily, changing your password regularly lessens your chance of being breached. You know what they say, “it’s harder to hit a moving target.”
Step 5
Our last step is usually an afterthought if it’s done at all. Back up your data! For a nominal fee, there are plenty of Cloud services that will back up your data for you. There are also external devices like hard drives and flash drives that you can keep separate. (Quick Note: If using a hard drive or flash drive, remove it from your machine after the back-up is performed. Those devices can be hacked if plugged into your machine when it’s attacked.)
Data backup is so important. If you do get hit with a ransomware attack, there’s no need to pay a ransom if you can restore your data on your own. Like a savings account or Netflix stock, it’s something you wish you’d snapped up when you had the chance. Don’t be left in the cold.
Safety First
There’s no guarantee that you’ll be perfectly safe for the life of your online presence, but if you follow the tips above you’ll reduce your chances of being a victim. And if you do happen to get attacked, the tips above can reduce the severity of the attack on your life. A little bit of diligence can go a long way.
For a list of ransomware attacks that have already taken place in 2019, you may click here. We have also created a map, see below, of the ransomware attacks that have taken place in the U.S.