The New Normal
If we didn’t spend an enormous amount of time online before the pandemic, we certainly are now. Life has shifted. Laptops, tablets, phones, and all other internet connected devices are necessary tools for working and learning.
Our connectivity is keeping us productive while we keep apart. But part of the reliance on our devices is also the need to keep them secure. Hackers and cybercriminals are more active now than ever.
Earlier in the year, when everything changed, people went into problem solving mode. In countless cases, we saw a shift in the work and school environment without a major shift in security. This led to an increase in hacks, and, subsequently, attacks on businesses, schools, and government entities.
We’re still living the fallout of those early mistakes. As we progress, however, we are taking more measures to secure our devices and stay a step ahead of the cybercriminals. But are your devices secure? Are you doing everything you need to do to keep them safe?
Let’s take a look at 5 tips to make sure your devices, and your information, is kept private.
5 Tips For Securing Your Device
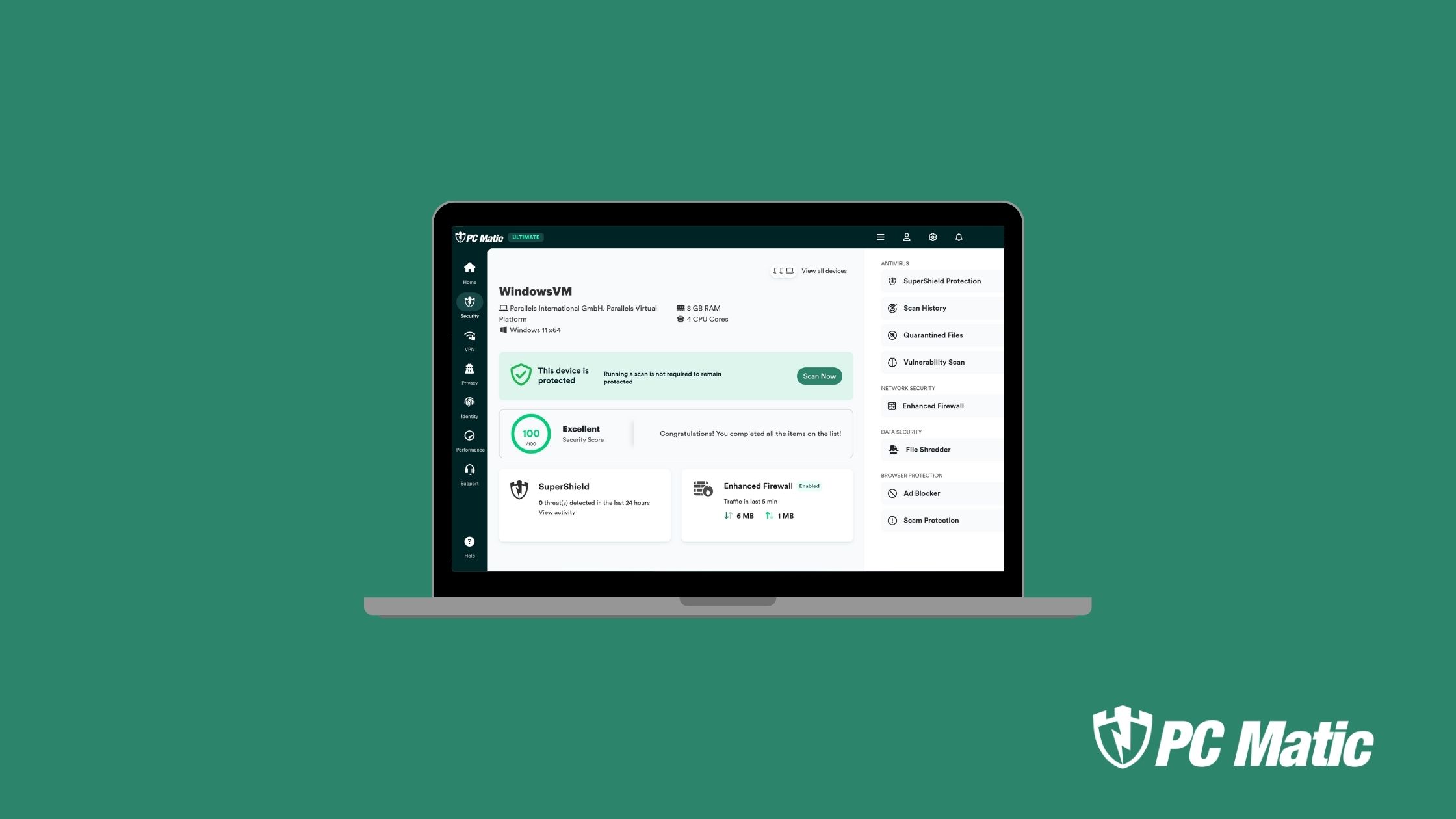
First, install a protective antivirus solution. Cybercrime is evolving, but so are our defenses. The idea that you can safely check email, surf the net, or connect via a teleconferencing service without protection is just not an option. There are too many ways a machine is vulnerable.
And remember, you get what you pay for. Free solutions may sound great, but they aren’t built as strong. Additionally, most of them mine your data and sell it. Hey, they have to make money somewhere!
Second, keep yourself educated. Everyone using a device should have cybersecurity training. While a quick web search yields tons of results for adults, educating kids on cybersecurity may be a bit harder. Consider a program like this one from FBI kids.
Next, set up scheduled scans. Your antivirus product should allow you to do this. If you aren’t sure how, reach out to them. They can help you set up regular scans for all your devices.
The fourth step is to change your passwords. You may be rolling your eyes. I know we talk about this a lot. But passwords are frequently compromised and sold on the dark web. Changing them means that you make the stolen information worthless.
Finally, keep your devices updated. Checking for regular updates on all your operating systems will keep you protected with the newest patches. Remember, ransomware is evolving and protection with it. It only keeps you safe if you have those evolved updates installed.
How PC Matic Is Helping
PC Matic is helping schools of all sizes take a cost-effective step towards
preventing rapidly growing ransomware demands and devastating privacy
breaches. In an effort to increase cybersecurity for remote learning, PC Matic is offering select K12 customers – free cybersecurity protection for staff and students using personal devices to work and learn from home.
Visit pcmatic.com to learn more!
We want you and everyone around you to stay safe. PC Matic realizes that finances can be tight right now, so we want to do all we can in this current environment. Do you know an educator? Let them know that PC Matic is here to help.
As we continue to navigate our new landscapes, we have to keep a watchful eye on our security. Let us know on our socials how you continue to #BeCyberSmart this National Cybersecurity Awareness Month.
As always, stay safe out there.