The digital age has become more advanced over the years. Since the Internet has evolved into different stages and versions, it too has paved the way for many of today’s latest innovations. From the Internet of Things (IoT) devices to cloud computing, it would have been considered a huge pipe dream if such things were mentioned more than a quarter century ago during the “dot-com” boom.
However, viruses have been around before the Internet has ever been introduced to the world. From the so-called “Creeper” self-replication computer virus created in 1971 to the “Brain” developed 15 years later, no one knew that such cyberattacks could create such chaos or evolve in the ways they are being distributed. Nevertheless, antivirus software was created to safeguard computers from viruses that would otherwise render them useless.
As technology evolved, so did the cyber threats. Thus, the question to be asked is “is an antivirus worth it in 2024?”. The short answer is yes. But there’s a caveat: it might not be enough.
That’s why in this guide, we’ll provide you with an in-depth explanation of why antiviruses are still a worthy investment both for individuals and businesses alike. Also, you will learn about cybersecurity threats and how you can go beyond antivirus software to ensure your computers are protected to the max. This will be a lengthy but detailed guide – but we intend to make it enough to cover our bases as much as possible. Let’s begin.
The cybersecurity threats of 2024: Where are we right now?
Many tech companies have their own predictions regarding the cybersecurity threats that exist in 2024 beyond the typical viruses, malware, ransomware, and so on. Some of them are more sophisticated than others. As mentioned, cybercriminals are always targeting every bit of the currently existing technology that exists.
Their main goal is obtaining sensitive data and selling it to the highest bidder. As a result, many will fall victim to identity theft and endure a painful process to fix the situation. Here are some possible cybersecurity topics that we believe are part of the conversation now and in the coming years:
More IoT devices being used
It should surprise nobody that IoT devices are growing in popularity. With so many different devices and services reaching the market, they serve a unique purpose for its end users. These include but are not limited to the following:
- Smart home devices: These include devices that turn on your lights, adjust your room temperature, and operate your home security system. They are controlled by touches on your smartphone or by the sound of your voice. You have full control of your home any place, any time – all without setting foot inside your home.
- Wearable devices: Apple Watches, FitBits, and similar devices are examples. This allows you to track your vital signs, fitness stats, and much more. These may also be included for those who are dealing with medical conditions and use the data that is monitored by themselves and their medical care providers.
- IoT for businesses and industries: These devices are used by business owners and industries for various purposes. They include keeping track of analytics for their production line, accounting for their daily business activities, and so much more. Many of them are connected to the cloud to ensure that they can be accessible anyplace and any time so long as they have the access credentials.
IoT devices may serve a purpose. However, what many don’t realize is that there are various entry points that cybercriminals can exploit with just the right skill and tools. Amongst the concerns with IoT devices include infringement on privacy policies and data breaches.
There is no denying that the number of IoT devices will continue to rise. Therefore, a protective solution to ensure maximum coverage against cyberattacks will be possible.
Cloud services are also a target of attacks as well
In recent years, cloud services have provided a huge convenience opportunity for many users. This includes providing them a place to store business data, create infrastructures with reduced use of physical hardware, and so much more. As such, cloud computing services through Amazon Web Services (AWS), Microsoft, and others have offered various advantageous solutions.
Despite this, cybercriminals have been creating threats to such cloud-based services. These include a reduction of control and visibility, misconfigurations, vulnerable applications, issues with data compliance policies, and so much more. The slightest misstep or misuse of cloud services can spell trouble for individuals and even businesses – especially those who have a responsibility to protect the sensitive data of others like their customers.
It is important for businesses that rely on cloud services to implement an antivirus software that provides you with the extra layers of protection needed. Once installed, you still need to do your part to make sure the data you store is protected.
Meaning you need to perform the best practices while following compliance measures regarding data. This also includes the regulations that are designed for specific industries and the jurisdiction you’re in (i.e – GDPR in the European Union or if you have customers that reside in the zone). Training your employees to be vigilant for any potential cybersecurity threats and performing best practices should also be recommended.
AI and Machine Learning: Their role in cybersecurity solutions
The digital age has ushered in the era of AI and machine learning. Of course, there have been valid concerns about AI and how it’s being used. Rest assured, 2024 could be the year where AI and machine learning may prove itself to be beneficial in the world of cybersecurity.
AI and ML have plenty of abilities that go beyond what humans can do. Needless to say, it offers a solution that could benefit our lives in terms of the tasks we perform and more. In terms of cybersecurity, AI and ML may be designed to improve the efficiency of security when it comes to our computers.
Cybersecurity professionals will be able to utilize the power of AI and ML to ensure they stay ahead of the curve of cybercriminals. Yet, who is to say that the cybercriminals themselves are looking to utilize the power of AI and ML to create what may be a weapon of mass cyber destruction? This could be a valid concern that can still be addressed so that AI and ML can be used for good while being restricted of its abilities to do harm.
The “Zero Trust” model
One cybersecurity model that has gained steam is the “Zero Trust” model. In short, this model assesses everything as a threat. Meaning the device you use and yourself may be a potential cyber attack – hence the concept of “zero trust”.
Needless to say, it’s a unique idea that has gained popularity amongst its users. The object of the model is that it emphasizes identity verification and continuous monitoring of user activity. When it comes to cybersecurity, this model can really make a strong case as an excellent protection option for users.
Threats both internal and external will be detected and neutralized. Meanwhile, the “zero trust” model can also monitor and protect the network itself and the lateral movements. It may sound like an excellent option against cyberattacks and even situations that can be triggered by human error (which accounts for over 90 percent of how they occur in the first place).
The only real downside to Zero Trust cybersecurity is the burden it imposes on the end user. PC Matic is the only solution available for consumers that includes fully automated “zero trust” protection through our patented Global Allowlist.
The emphasis of multi-factor authentication (MFA)
There is no such thing as too much when it comes to cybersecurity protection. Thus, it should be emphasized that multi-factor authentication (MFA) is still one of the most reliable measures you can put into place. Passwords, the devices that are recognized as “standard”, and the biometrics are one thing. Yet, MFA is designed to confirm to make sure it’s really the same person gaining access.
MFA for its part should be a non-negotiable security measure for individuals and businesses. In fact, those who don’t have something like this in place should be considered “high risk”. Many are confident in MFA’s protection abilities, making it a strong case for those who don’t implement it to do so as soon as possible.
Expect threats to evolve continuously
As we have mentioned earlier, the cybersecurity threats evolve along with the advancement of technology. Nonetheless, they can also be persistent and evolve into various versions of themselves. For example, take a look at ransomware – which could take the shape of something that is more sophisticated while setting its sights on individuals and businesses alike.
At this point, an antivirus software with ransomware protection could only do so much. Even sneaky and skillful cybercriminals may find a workaround. Therefore, backing up your data on a regular basis – even on a cloud-based solution – should be highly recommended, if not an unwritten requirement. If anything, it’s your best line of defense against a cyberattack aiming to hold your files and data hostage until you pay them ransom.
Meanwhile, it is imperative that you make your employees aware of any other cybersecurity risks including malware, viruses, phishing, scam emails and links, and so much more. Once again, human error accounts for many of these cyber attack issues. Awareness and educating your employees on cybersecurity measures and precautions are a must for any organization.
Recognizing and eliminating inside threats
External threats are often the focus of cyberattacks. Internal or insider threats should also be considered a legitimate concern. They can exist both with or without intent. Human error is considered an insider threat.
Insider threats may seem like a challenge to curb. The reason for this is that no one knows if anyone has malicious intent to launch a cyber attack from the inside. In terms of preventing human error, the best line of defense is awareness and training to help avoid such cyberattacks from being triggered in the first place. This includes businesses training employees on how to identify cybersecurity threats using cyberattacks against other companies as an example.
Visual examples such as a legitimate email versus one containing a malicious link should be used for training purposes. Demonstrations of distinguishing the good from the bad in the cyberworld should also be part of the education as well. It may seem overwhelming at first, but no one has to be a computer master to understand and recognize cybersecurity threats.
To reiterate up to this point, an antivirus software in 2024 is a worthy investment. As they come in different versions with various capabilities such as protection against various threats, they can also provide additional features for better security. For example, PC Matic has taken things a step further in protecting those from identity theft by including IdentityForce in a special service plan.
Antivirus software and the evolution of cybersecurity threats
While antivirus software was created more than a half century ago, it wasn’t available to the public until much later. Such software would reach the market as early as the late 1980s and early 1990s, which were available as hardware disks that can be inserted in computers.
As computer technology evolved, antivirus software would be available in the proper forms. For example, the software would go from being deployed via hard disks to CD-ROM. Later on, they would become available as digital downloads that only required an install rather than popping a CD into the computer.
Still, it was vital to stay ahead of the game when it came to avoiding viruses, malware, and other cyberattacks. With the introduction of the Internet, it wasn’t until the 2000s when the threat of such attacks increased the amount of concern amongst computer users. More than a quarter century later, everything has changed in terms of cyberattacks and the systems that are designed to deter them.
A virus created in the early 2000s would not stand a chance against an antivirus software that is updated for today’s modern standards. For that reason, cybercriminals have created even more sophisticated ways to compromise computer systems and render them useless. All while being able to acquire the data they typically find important such as identity and financial information.
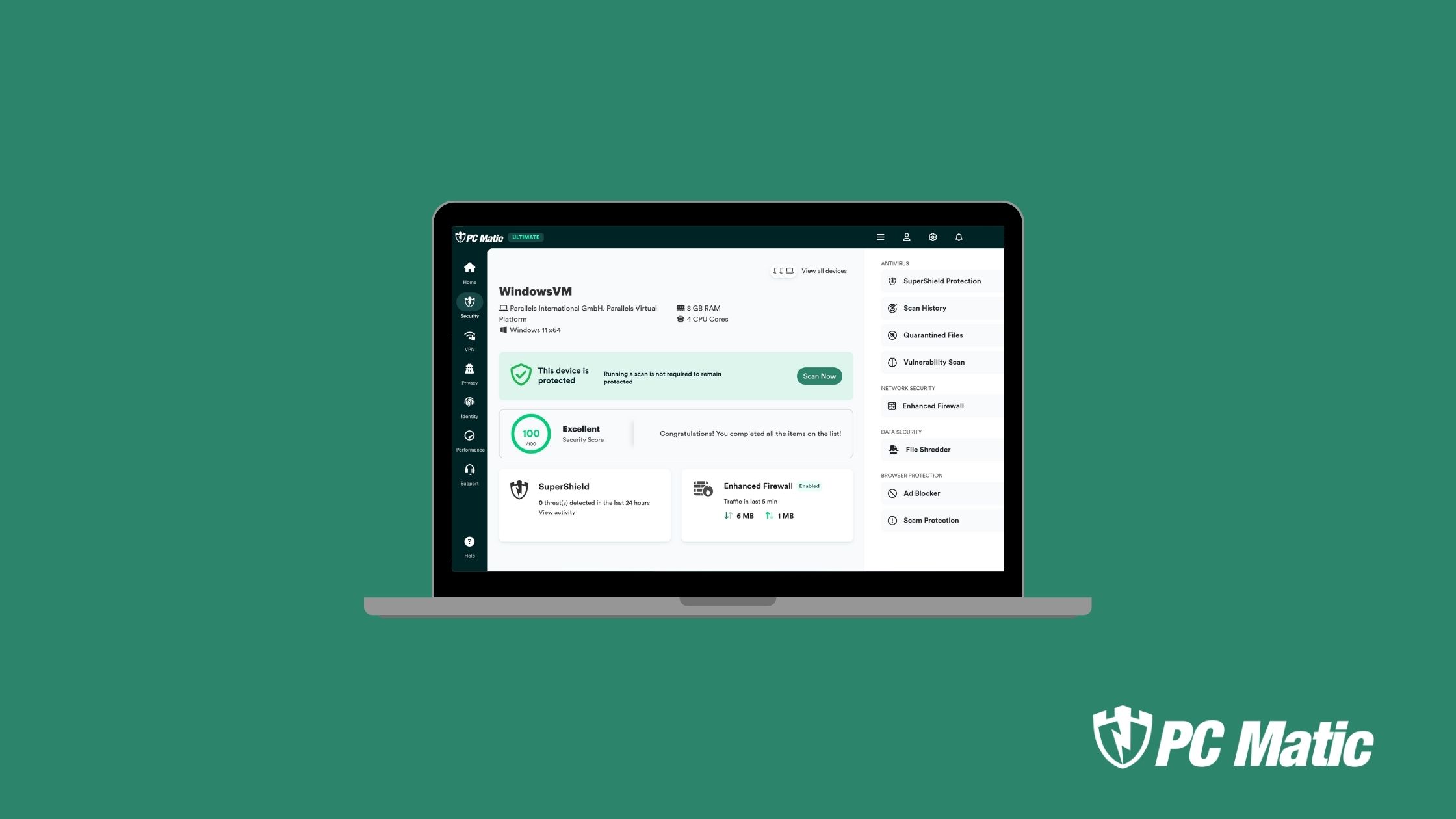
Today, antivirus solutions like PC Matic are considered to provide some of the best consumer protection available. Whether it’s something you install or a built-in antivirus solution like Microsoft Defender, you need to make sure it gives you the adequate coverage.
With newly created attacks, antivirus software creators would always find ways to deter them. How have they evolved over the years up until the present? Here are some of the different aspects antivirus software have adopted:
Behavioral and heuristic analysis
Antivirus software has the ability to analyze user behavior in its part to determine if certain applications are considered malicious. For example, they dive deep and analyze factors such as activity, file access, registry changes, and network connections – all of which to ensure whether it’s standard or suspicious behavior.
As such, the heuristic analysis looks out for any behavior that appears to be a pattern that only malware can display. Thus, if a program you download or intend to run displays that behavior, the antivirus software will notify you that something is considered potentially malicious.
The use of cloud technology
Cloud-based technology is more than a blessing for those who use it for data storage and infrastructure. It also has abilities to protect your computer as well. The identification and response to new threats is much quicker and may not require any significant software updates.
This means it can run behind the scenes and do its regular role at all times. It is always ready to detect and stop any cybersecurity threat in its tracks. Yet, it still requires a strong ally in end users to be vigilant of any threats that may be unfamiliar to the security software itself.
Machine learning
As mentioned earlier, AI and machine learning are both seen as potential technology to help fend off cybersecurity attacks. The algorithms used are designed and programmed to perform various responsibilities including pattern recognitions including what is considered normal or abnormal behavior. In terms of unfamiliar cyberattack strains, ML-based antivirus products can possess the ability to detect and block them, even if it’s an initial encounter.
As cybersecurity threats are newly created on a regular basis, smart technology could play a role in identifying and blocking threats by default. Even if it’s the first time such threats attempt to make contact with your computer system. This gives many individual and business users the confidence and peace of mind knowing their computers are safe, even if an attack triggered by human error is deterred.
What are the cybersecurity threats that exist today?
There are plenty of common cybersecurity attacks that threaten computer systems used by both individuals and businesses today. As such, it is important to make sure an antivirus program and other antivirus tools like Bitdefender can provide you with all kinds of protection against online threats. Here are the cybersecurity threats to be aware of (along with why they should be taken seriously):
Malware
Malicious software – hence why it’s called “malware”. It can appear as a program, app or a code that is designed to attack a computer, server, or network. They also come in numerous forms including viruses, spyware, trojan horse attacks, bots, keyloggers, ransomware and even cryptojacking.
All told, there are around a dozen different versions of malware attacks that exist. Each with their own unique capabilities. For example, a trojan horse attack appears like software that looks like the real deal. Often, they rely on social engineering to be successfully installed.
Once installed, the trojan will launch its intended attack. Some of these malware types not only affect computers but have the ability to infect mobile devices as well. These can be delivered by way of malicious downloads and vulnerabilities that exist within the operating system or an unsecure WiFi network.
DoS attacks
This is called a Denial of Service (DoS) attack. When one is activated, a computer user will not be able to perform seemingly simple tasks such as accessing websites, using email services, or other resources. Another form is a DDoS attack, which originated from multiple systems – making it more challenging to deal with compared to a regular DoS attack. Though DoS and DDoS attacks may not threaten data, it can lead to a loss of ability of using a computer along with its functions being compromised.
As a result, the inability to use a computer system can lead to a loss of time, money, and resources. It will more often lead to business operations facing disruptions until the issue is resolved.
Phishing
This type of cyberattack has been around for a long time. Phishing attacks are found in emails, text messages, pop-ups, malicious apps, and social media posts or comments (with an included link). It will rely on social engineering to get someone to click the link that will lead to sharing sensitive information or downloading a malicious program that will install viruses.
There are different types of phishing that exist, each with their own unique list of targets. For example, cybercriminals can target executive level employees of a company with the intent of stealing financial or other sensitive information by accessing their computers. This is known as “whaling”.
Other types include “spear phishing”, which targets individuals and businesses by way of email. SMiShing uses text messages to fool an individual to click on the link or share data. A cybercriminal will claim to be from your bank, an online business, or even a government entity like the IRS and ask you for such information.
Because of this, you want to take the necessary precaution to contact the necessary business. For example, if the text claims to be from your bank, you want to call them to verify if the message is real or a SMiShing attempt. The same concept applies if you receive an email claiming to be Amazon or some other familiar online business you have patronized on a regular basis.
Vishing doesn’t need the Internet – but it’s still a type of attack that uses phone calls or voice messages claiming to be calling as a legitimate organization. They will ask for sensitive information such as your bank account or passwords. As you may have noticed, an antivirus software may not be able to thwart an attack that is done over the phone.
That’s why it is always important to be extra vigilant. While antivirus programs can do so much, there are some things it may be unable to do – even by itself.
Spoofing
We’ve touched on spoofing a bit when we talked about different phishing attacks. Cybercriminals who claim to be from a trusted source target people in an effort to have them hand over any sensitive information. The most common are domain and email spoofing – which either can look legitimate to the untrained eye. If you look closer, you may notice some subtle differences.
One in particular is the typography of certain letters. For example, an “a” in the Cyrillic alphabet will look dangerously close to one that is shown in the Latin alphabet. With sharp observation skills, it will make a huge difference between avoiding a cyberattack or becoming a victim of one.
If in doubt, it’s important to call the organization itself. For example, if you receive an email claiming to be from Amazon, you can call their customer support to notify them of the suspicious email you have received. They can confirm whether or not the email is real or not.
Even apps looking like the real deal could be a form of spoofing. That’s why it is important to do research on whether or not it’s real before opening it.
Code injection attacks
This involves malicious codes being injected into a computer or network. The goal is to get the target to change its functionalities. One such attack is the SQL injection attack, in which hackers can use SQL codes to extract any important information from a database. In turn, they can alter the data, steal it, or even delete it completely.
Another code injection attack is cross-site scripting or XSS. This occurs when a malicious code is injected into a trusted website, which can lead to hackers stealing any sensitive information or even impersonating a user. Websites that host message boards, blogs, and other forms of communication are considered the most vulnerable to such attacks.
Identity-based attacks
These are considered one of the most challenging attacks in terms of detection. The major reason is that it is difficult to distinguish the real user’s behavior and the hacker’s (given the latter is using security tools and measures). There are various types of attacks that exist – which antivirus software may not be enough to take care of the problem on its own.
These attacks include a Man-in-the-Middle attack (MitM), which the hacker eavesdrops on a conversation with the intent to collect sensitive data. Social engineering can be involved in this kind of attack as well. One way they perform this is by setting themselves up as a legitimate public WiFi hotspot.
They even spoof the name, but with some subtle differences. In a public place, you may notice two different WiFi connections with the same name. In reality, there should only be one.
If someone connects to the WiFi network set up by the attacker, that’s when it all begins. To prevent falling victim to an attack, it may be wise to consider using a VPN. Some antivirus programs may offer a VPN as part of its package deal to customers.
A VPN will mask the IP address your operating from and protect you by way of an encrypted network. You will be able to surf the web safely without any risk of being caught in the “middle” of an MitM attack.
Other identity-based attacks include brute force attacks, credential harvesting, and even a downgrade attack – which uses your operating system’s backwards compatibility features. These attacks are examples while a trained eye and being extra cautious will be the best course of action rather than relying on an antivirus alone.
Supply chain attacks
Commercial and industrial organizations will often be targeted by supply chain attacks – both in the software and hardware sense. A software supply chain attack will act in a similar manner to code injection attacks while a hardware supply chain attack will attack an infrastructure’s physical components.
Regardless, the intent and purpose is still the same. These attacks will lead to a disruption of business and critical functions that play a role in the supply chain process. It could even create an effect that can cause a loss of time, money, and peace of mind.
IoT attacks
As mentioned earlier, the use of IoT devices and the number available is increasing. With that, the threat of IoT attacks is taken more seriously considering that it can lead to hijacking the control of one’s device, data theft, and even get linked to other infected devices that can cause more havoc.
Factors to consider before purchasing an antivirus program
With so many antivirus solutions on the market, choosing the right one is a challenge. That’s why you need to take a few factors into consideration that will help you decide in a well-informed manner. If you are serious about protecting your individual or business computer system, choosing one that fits your critical needs is key. Here’s a look at what to consider:
Your budget
The price of an antivirus program can be a deciding factor. Because you want to stay within your budget. However, trying to save extra money may be more of a curse than a blessing. Here’s the thing, some cheaper options can do the basic functions but may not give you advanced protection.
What are the factors that play a role in price? This includes the amount of devices it covers, cloud backup storage space (if available), and other tools and extra features. The lowest price package will cover the basics in terms of protecting you from cybersecurity threats for at least one device.
If you have any additional devices that need coverage, you’ll need to pay a higher price. Get an estimated number and choose the one to the closest limit (i.e – if you have four devices, choose a package that can cover up to five). Whether your PC is a Microsoft and an Apple iPad on the go, you can still get the same coverage regardless.
Keep in mind that a paid antivirus software offer not just basic protection but additional security features where you can pay monthly or annually. Some may be available for a one-time purchase. Determine how much you are willing to spend monthly or annually on antivirus protection. Just because you pay for a free version, doesn’t mean you’re going to compromise a level of protection since it can cover the basics (which will be good enough for most users).
Is it for individuals or businesses?
While some of the concepts of an antivirus are the same, there may be some differences. A software for individual coverage will differ from a solution tailored for businesses. This can be due to the fact that businesses use a much larger scale, robust setup. As such, they may require a solution that will give them protection for their computers, networks, and so on.
Such solutions made for businesses would be overkill if installed on devices designed for personal use. If you are an individual, choose an antivirus software that will handle devices made for such use. On the other hand, find a business-style antivirus that will give you all kinds of protection against cyberattacks.
What features address your most critical needs?
Paying more does give you additional features. However, your most critical needs are more important than the price tag itself. With this in mind, you want to assess what you believe those needs are and match them with the features that are appropriate.
If you’re simply looking for protection against cyberthreats for one device, you can get away with purchasing the antivirus software that will address those needs. Of course, you pay a little more for other additional features that will be worth every penny if you need them as well.
Aside from the basic protections, you can get additional security features like spam filters, firewalls, anti-phishing tools, and so much more. Carefully weigh your options according to the critical needs you want addressed with the features that actually matter most.
Ease of use
Simply put, you want an antivirus where you have an easy time using it. You want the dashboard to be a simple layout. It also helps that you be able to navigate it with ease.
You will be able to know where everything is including the button that runs a scan. Also, you’ll be able to navigate the menu easily so you can use the other features.
How well does it perform (and how reliable is it)?
Performance and reliability are two major things that can make or break an antivirus solution. The better it performs and the more reliable it is, the more popular it might be. No one wants to use one that is unreliable and performs below expectations. Especially in a time when cyberattacks are taken more seriously than ever.
Reliability and performance should go beyond scanning at one click of the button. It should be constantly in operation in the background monitoring any threats that arise. The quick response ensures that it can be reliable and perform the best while you’re using your computer for individual or business purposes.
It can also detect potential threats, reminding you beforehand of whether or not such links, websites, and other online assets should be trusted. Remember that you make the decision to decide what could be “whitelisted” and what could be denied on your computer. Antiviruses do so much, but you can make it more effective by being more vigilant.
Is it compatible with your operating system?
Compatibility is something that tends to be overlooked at times. It may be wise to make sure your computers use the most recent operating systems like Windows 11. If you are using Windows 10 for the time being, no need to worry – antivirus programs can provide protection for those still using past operating systems (if applicable).
However, other operating systems of the past should not be used. There are various reasons why. For one, today’s newer versions of antivirus solutions may not be compatible with older operating systems like Windows XP, Windows Vista, etc. To make things a bit more bleak, Microsoft has even phased out security updates for these operating systems, making them vulnerable to newer forms of cyberattacks.
When looking for an antivirus software, check which operating systems it can work with. Compatibility will make it easier to install and in turn provide your computer system with the protection it needs. Also, you want to make sure it’s compatible with various web browsers like Microsoft Edge, Google Chrome, Firefox and others. If you are using mobile devices, make sure it’s compatible with Apple and Android.
If an antivirus works with both Microsoft and Apple devices for instance, they can be quite versatile. As mentioned, you can add a Microsoft PC and an Apple device on the list of what can be covered. So long as they meet the compatibility requirements, you can protect as many devices as you wish depending on the antivirus package you choose.
Tips for maximum protection against cyber attacks
Even though antivirus programs can perform the necessary tasks it can, it needs all the help it can get to make sure your computer is protected. For this reason, we provide you with these tips that you can follow to ensure that cyber attacks are completely avoided. They include the following:
Stay aware of any cyber threats
Awareness is always important when it comes to knowing which cyber threats are out there. Unfortunately, we learn of these when it has already claimed a “victim”. Soon enough, we know about the damage done, what was affected, and so much more.
Stay in the loop about cyber security threats by subscribing to blogs or email lists related to cyber security. No one better than cyber security experts themselves to give you a heads up about possible threats before a cybercriminal launches it, making it too little and too late.
Implement parental controls
If you have children that use a computer or laptops, you want to activate any parental controls. This will allow them only to access certain parts of the computer while restricting them from others. These include but are not limited to various websites that may be unsafe for viewing (where such threats could arise).
Perform regular scans
Regular scans or av-test can be automated or done manually – whichever you prefer. You can use your antivirus or even additional tools like Malwarebytes to ensure that your computer is free from any potential threats. When setting up your antivirus, you can automate a schedule where it can run regular scans for you – be it daily, weekly, monthly, or a custom time frame.
Download mobile apps from appropriate places
If you want to add an antivirus app or anything else, you need to make sure it’s from appropriate places like Apple’s App Store or Google Play (if you are using an Android device). Be sure to switch off a feature that may allow you to download apps that are not available on these marketplaces. Downloading such apps outside of the App Store or Google play is risky and could lead to infections on your device.
Educate your team members and employees
If you are a business owner or manager, chances are you and your employees are using computer systems that are critical to your business operations. Cyberattacks can bring it all to a grinding halt in the blink of an eye. It could be due to someone clicking on an unsuspecting link.
Plan training sessions that will teach your employees the dangers of cyberattacks on business computers. Especially when they serve a credible threat to the data you keep on your servers and storage devices. It also helps to provide them with visual examples of what to spot if something appears suspicious.
Show them certain characteristics and features that are prominent with cyberattacks. Especially the examples that point out the most subtle features that get missed easily by untrained eyes. It takes sharp observation skills and positively identifies a potential cyber attack to save your business from the headaches and heavy costs it can face if such an event were successful.
Of course, educating yourself on these threats when using individual devices won’t hurt either. Cyber attacks are not exclusive to any kind of computer system, be it for individual or business use.
Comply with data regulations (if applicable)
If you are a business owner that handles sensitive customer data regularly, it is important you comply with the applicable regulations. These include regulations that are outlined by governing bodies and industries. For example, if you manage a doctor’s office, you need to make sure the data handling and storage is compliant with HIPAA regulations to ensure patient confidentiality.
Another example pertains to an eCommerce business that serves customers in the European Union. You must comply with the GDPR regulation for data protection and handling – regardless of where you may be in the world. Failure to comply with such regulations could lead to legal repercussions including fines and even lawsuits.
Protect yourself if using Public WiFi networks
Public WiFi is one of the largest hotbeds for cybersecurity attacks (especially MitM). Knowing the name of the network is one thing. However, noticing that there are two networks with the same name is a red flag.
If you run into this problem, this is an MitM waiting for its next victim. You want to notify the manager of the establishment you’re in regarding this situation. Regardless, it is important to protect yourself against vulnerabilities and attacks that can happen on a public network. Using a reliable VPN will be your best line of defense.
If in doubt, say something
This applies to any suspicious emails or text messages you may receive – even those claiming to be from a reputable business or organization. Get accustomed to the actual ways a business or organization will get in contact with you.
Right up front, they will be clear about the ways they contact you and the nature of the messages. One common disclaimer is that a business or organization will never email or text you asking for banking information or personal data. If you believe something seems off, contact the organization in question as soon as possible to discuss the email or message you received. It never hurts to double check whether or not it’s the real deal.
Conclusion
Antivirus is worth purchasing in 2024 as it has in the past. It will also be worth it in the future as well. Cybersecurity threats will still exist and you need effective protection against viruses, malware, and others. However, taking proactive measures like spotting potential issues, preventing insider threats, and educating your team members on identifying and getting rid of potential threats will take things a step further in making sure your computer system and devices are protected completely.