Troy Spetter at Edison High School
Often times we have customers reaching out to us to share their success stories. We love taking the time to highlight some of these customers. Listen to Troy, in his own words, tell you his PC Matic story.
Often times we have customers reaching out to us to share their success stories. We love taking the time to highlight some of these customers. Listen to Troy, in his own words, tell you his PC Matic story.
Subscribe to our newsletter to get cybersecurity tips & tricks and stay up to date with the constantly evolving world of cybersecurity.
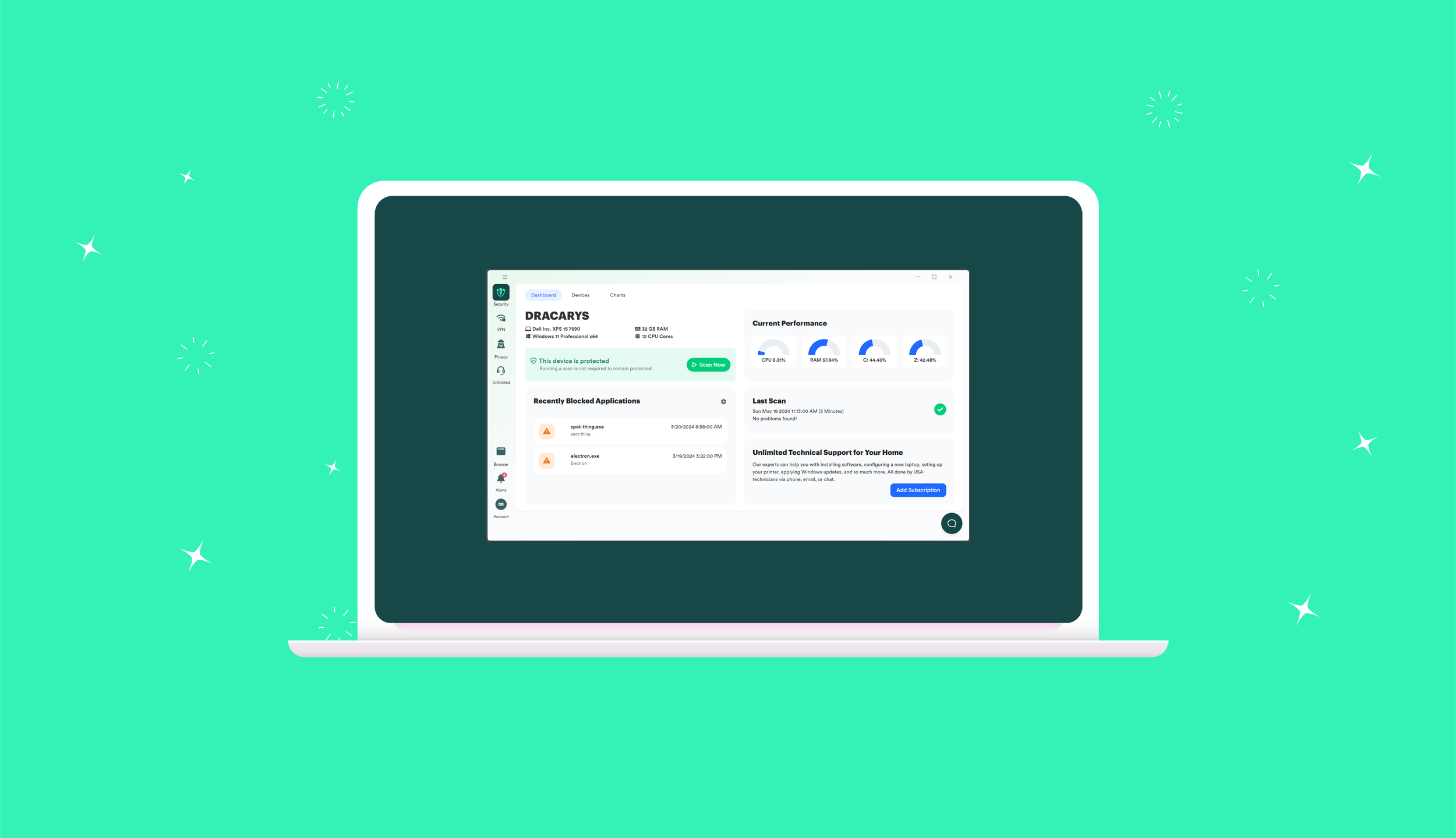
This year is an exciting one here at PC Matic, and it’s time to bring you in on the fun. Our teams have been hard

It’s just Hollywood, right? Movies can often leave you with an uneasy feeling, and Sam Esmail’s new film Leave the World Behind is no different.

The use of torrents has been a hot topic of debate for years, with some arguing that it’s a tool for piracy, while others defend