
Why Your Business Needs a “Default Deny” Strategy in the AI Era
A recent TIME article highlighted a sobering reality: cybersecurity threats are growing at an overwhelming pace, fueled by advanced AI and a corporate culture that

A recent TIME article highlighted a sobering reality: cybersecurity threats are growing at an overwhelming pace, fueled by advanced AI and a corporate culture that
Subscribe to our newsletter to get cybersecurity tips & tricks and stay up to date with the constantly evolving world of cybersecurity.

When discussing cybersecurity strategies like Zero Trust, it is easy to get lost in high-level theory. However, the most valuable insights often come from those

Zero Trust is a term that gets thrown around constantly in cybersecurity circles, often accompanied by confusion or intimidation. Is it a product? A single

It’s 3:00 AM. Your phone buzzes with a critical security notification. Is it a genuine ransomware attack in progress? Or is it the fifth false

It’s a statistic that sounds like a joke, but the punchline is a security nightmare. After decades of cybersecurity training, relentless warnings, and increasingly complex
One of the most common questions our support team receives is: “How do I know if my devices are actively being scanned?” It’s a great

In today’s landscape, modern cyber threats require a proactive approach. However, for many agencies, schools, and businesses, building a comprehensive Zero Trust framework can feel

As security professionals, we often classify parked or dormant domains as low-priority nuisances—digital litter that occasionally serves an annoying ad. That classification needs an immediate

The holidays are approaching, and the instinct is universal: wrap up the final tasks, set the “Out of Office” auto-reply, and shut down the computer—hoping
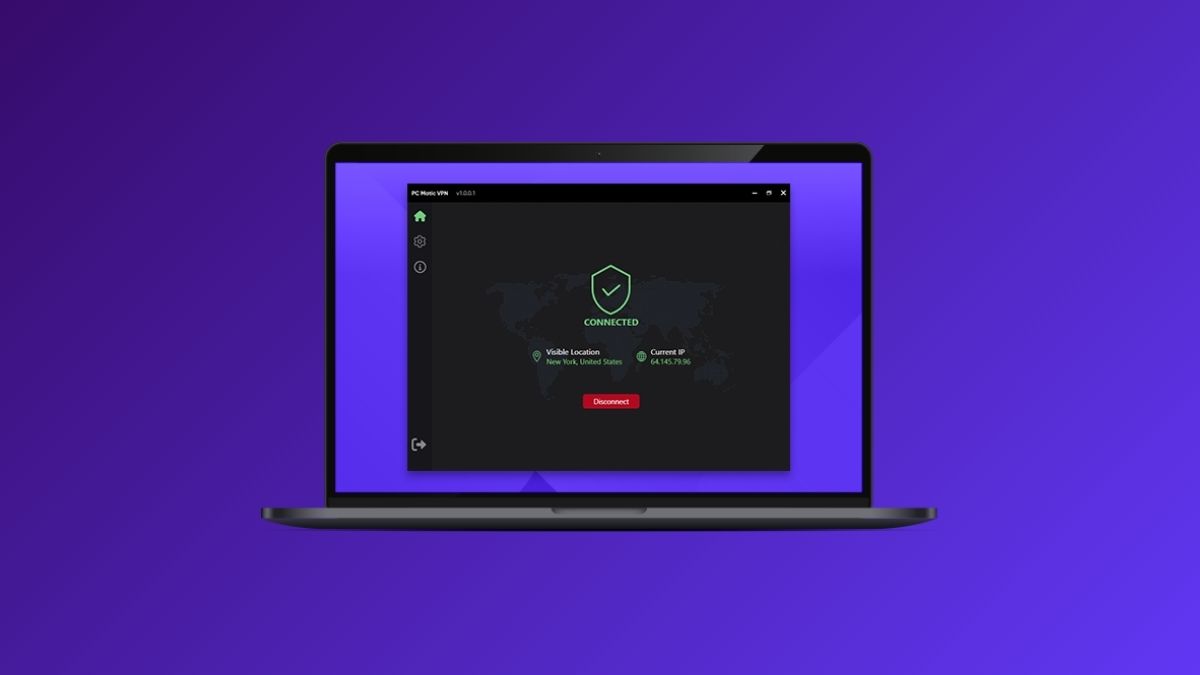
Today’s teams work from everywhere: offices, homes, hotels, airports, and coffee shops. Every connection outside a trusted network increases risk. A VPN keeps those connections