Ransomware is taking on a whole new approach to infecting victims…
Ransomware authors are now using voice message notifications to distribute the malware to unsuspecting victims. This is a new, advanced approach for these cyber criminals for one major reason. Everyone can receive voice message notifications, whether it is a business employee or a home user. The one caveat is that they must be using some kind of unified communications method such as Cisco.
Why is this more advanced than other forms of ransomware distribution? Hackers are able to avoid unsuccessful attempts to infect users who do not use the file types used to distribute other variants of ransomware by using the voice message notification method.
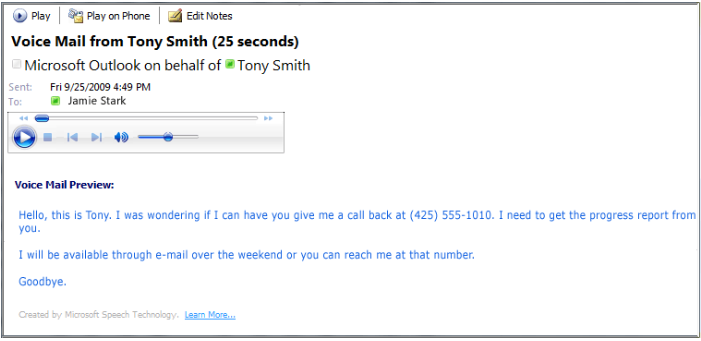
According to Internet Storm Center, the voice message notification looks like this:
Here is how you can avoid becoming a victim to these attacks. First, delete the email and call whoever it said the message was from, on your own. As previously stated in other posts, do not call the number identified in the email. It is advised you look up the phone number from another source to prevent calling a potentially falsified number within the email.




